Recommended Virus Software For Mac
- Recommended Virus Software For Mac
- Scan Mac For Virus Free
- Best Virus Protection For Mac
- Best Virus Software For Macbook
- Recommended Virus Software For Mac Windows 10
- Recommended Virus Software For Mac Windows 7
2. All versions of OS X since 10.6.7 have been able to detect known Mac malware in downloaded files, and to block insecure web plugins. This feature is transparent to the user, but internally Apple calls it 'XProtect.' The malware recognition database is automatically checked for updates once a day; however, you shouldn't rely on it, because the attackers are always at least a day ahead of the defenders.
Jun 05, 2020 Here are my picks for the best free Mac antiviruses in 2020: Sophos — #1 pick for 2020.; Avira — Comes with real-time malware protection and it’s easy to set up and use.; Bitdefender — Lightweight software. Does some great quick and easy Mac scanning. Malwarebytes — Only malware scanning and removal.; TotalAV — Great tools for cleaning and optimizing Mac performance. Jul 16, 2020 Gsearch is a browser Adware hijacker for macOS computers. Gsearch is compatible with many browsers including Chrome, Safari and Firefox.
The following caveats apply to XProtect:
- It can be bypassed by some third-party networking software, such as BitTorrent clients and Java applets.
- It only applies to software downloaded from the network. Software installed from a CD or other media is not checked.
Gatekeeper doesn't depend on a database of known malware. It has, however, the same limitations as XProtect, and in addition the following:
- It can easily be disabled or overridden by the user.
- A malware attacker could get control of a code-signing certificate under false pretenses, or could simply ignore the consequences of distributing codesigned malware.
- An App Store developer could find a way to bypass Apple's oversight, or the oversight could fail due to human error.
For the reasons given above, App Store products, and other applications recognized by Gatekeeper as signed, are safer than others, but they can't be considered absolutely safe. 'Sandboxed' applications may prompt for access to private data, such as your contacts, or for access to the network. Think before granting that access. OS X security is based on user input. Never click through any request for authorization without thinking.
4. Starting with OS X 10.8.3, a third layer of protection has been added: a 'Malware Removal Tool' (MRT). MRT runs automatically in the background when you update the OS. It checks for, and removes, malware that may have evaded the other protections via a Java exploit (see below.) MRT also runs when you install or update the Apple-supplied Java runtime (but not the Oracle runtime.) Like XProtect, MRT is presumably effective against known attacks, but maybe not against unknown attacks. It notifies you if it finds malware, but otherwise there's no user interface to MRT.
5. XProtect, Gatekeeper, and MRT reduce the risk of malware attack, but they're not absolute protection. The first and best line of defense is always your own intelligence. With the possible exception of Java exploits, all known malware circulating on the Internet that affects a fully-updated installation of OS X 10.6 or later takes the form of so-called 'trojan horses,' which can only have an effect if the victim is duped into running them. The threat therefore amounts to a battle of wits between you and the malware attacker. If you're smarter than he thinks you are, you'll win.
That means, in practice, that you never use software that comes from an untrustworthy source, or that does something inherently untrustworthy. How do you know what is trustworthy?
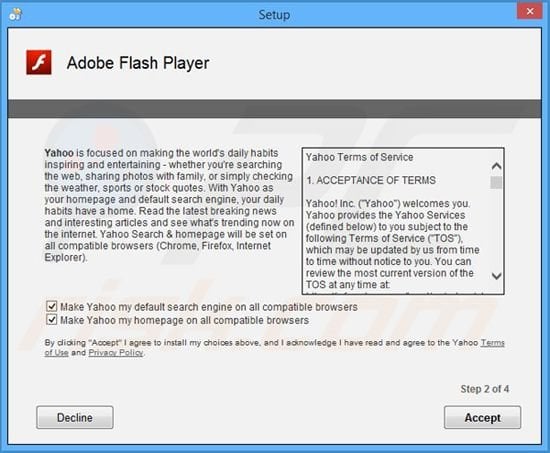
- Any website that prompts you to install a “codec,” “plug-in,” 'player,' 'extractor,' or “certificate” that comes from that same site, or an unknown one, is untrustworthy.
- A web operator who tells you that you have a “virus,” or that anything else is wrong with your computer, or that you have won a prize in a contest you never entered, is trying to commit a crime with you as the victim. (Some reputable websites did legitimately warn visitors who were infected with the 'DNSChanger' malware. That exception to this rule no longer applies.)
- Pirated copies or 'cracks' of commercial software, no matter where they come from, are unsafe.
- Software of any kind downloaded from a BitTorrent or from a Usenet binary newsgroup is unsafe.
- Software that purports to help you do something that's illegal or that infringes copyright, such as saving streamed audio or video for reuse without permission, is unsafe. All YouTube 'downloaders' are in this category, though not all are necessarily harmful.
- Software with a corporate brand, such as Adobe Flash Player, must be downloaded directly from the developer’s website. If it comes from any other source, it's unsafe.
- Even signed applications, no matter what the source, should not be trusted if they do something unexpected, such as asking for permission to access your contacts, your location, or the Internet for no obvious reason.
Fortunately, client-side Java on the Web is obsolete and mostly extinct. Only a few outmoded sites still use it. Try to hasten the process of extinction by avoiding those sites, if you have a choice. Forget about playing games or other non-essential uses of Java.
Recommended Virus Software For Mac
- Their design is predicated on the nonexistent threat that malware may be injected at any time, anywhere in the file system. Malware is downloaded from the network; it doesn't materialize from nowhere.
- In order to meet that nonexistent threat, the software modifies or duplicates low-level functions of the operating system, which is a waste of resources and a common cause of instability, bugs, and poor performance.
- By modifying the operating system, the software itself may create weaknesses that could be exploited by malware attackers.
8. ClamXav doesn't have these drawbacks. That doesn't mean it's entirely safe. It may report email messages that have 'phishing' links in the body, or Windows malware in attachments, as infected files, and offer to delete or move them. Doing so will corrupt the Mail database. The messages should be deleted from within the Mail application.
A Windows malware attachment in email is usually easy to recognize. The file name will often be targeted at people who aren't very bright; for example:
Install VMware Tools on macOS Virtual Machine. After you’ve done this, you can work or do whatever you’ve in mind with the machine. But unlikely, you won’t have the important but optional things like full-screen resolution, enhanced graphics, and smooth run even after assigning the most resources. MacOS Mojave Final APFS by Geekrar (One Full – Google Drive) — With macOS Mojave updating after some time, we’ve updated macOS Mojave VMware & VirtualBox Image that is the latest for now. This version is as well as installed as the previous version. There are multiple important reasons why you should keep your Mac OS Version up to date; with the main reason being security. For example, in this last version of Mojave one of the facilities that plays a crucial role in keeping your Mac safe is Oversight, and the latest update means that just like with your iPhone and iOS, it will alert you when an application wants permissions to hardware. Software updatrs of macos in vmware. Install MacOS Mojave on VMware on Windows. In order to install MacOS Mojave on VMware, you will need to have MacOS Mojave Vmware Image like download MacOS Mojave 10.14 VMware Image. Moreover, download and install VMware Workstation/Player and in last you will need to install 7Zip/ Winrar to extract the Macos Mojave vmdk file. So, I will guide you all the steps one by one in below.
♥♥♥♥♥♥♥♥♥♥♥♥♥♥!!!!!!!H0TBABEZ4U!!!!!!!.AVI♥♥♥♥♥♥♥♥♥♥♥♥♥♥.exe
ClamXav may be able to tell you which particular virus or trojan it is, but do you care? In practice, there's seldom a reason to use ClamXav unless a network administrator requires you to run an anti-virus application.
We design Mac hardware and software with advanced technologies that work together to run apps more securely, protect your data and help keep you safe on the web. And with macOS Catalina available as a free upgrade, it’s easy to get the most secure version of macOS for your Mac.*
Apple T2 chip.
The next generation of security.
The Apple T2 Security Chip — included with many newer Mac models — keeps your Mac safer than ever. The Secure Enclave coprocessor in the Apple T2 chip provides the foundation for Touch ID, secure boot and encrypted storage capabilities. Touch ID gives you a seamless way to use your fingerprint to unlock your Mac, fill passwords in Safari and make purchases with Apple Pay. Secure boot helps ensure that you are running trusted operating system software from Apple, while the Apple T2 chip automatically encrypts the data on your Mac. So you can be confident knowing that security has been designed into the architecture of your Mac, from the ground up.
Apple helps you keep your Mac secure with software updates.
The best way to keep your Mac secure is to run the latest software. When new updates are available, macOS sends you a notification — or you can opt in to have updates installed automatically when your Mac is not in use. macOS checks for new updates every day, so it’s easy to always have the latest and safest version.
Protection starts at the core.
The technically sophisticated runtime protections in macOS work at the very core of your Mac to keep your system safe from malware. This starts with industry-standard antivirus software built in to block and remove malware. Technologies like XD (execute disable), ASLR (address space layout randomisation), and SIP (system integrity protection) make it difficult for malware to do harm, and they ensure that processes with root permission cannot change critical system files.
Download apps safely from the Mac App Store. And the internet.
Now apps from both the App Store and the internet can be installed worry-free. App Review makes sure each app in the Store is reviewed before it’s accepted. And Gatekeeper on your Mac ensures that all apps from the internet have already been checked by Apple for known malicious code — before you run them the first time. If there’s ever a problem with an app, Apple can quickly stop new installations and even block the app from launching again.
Stay in control of what data your apps can access.
Apps need your permission to access files in your Documents, Downloads and Desktop folders as well as in iCloud Drive and external volumes. And you’ll be prompted before any app can access the camera or mic, capture keyboard activity, or take a photo or video of your screen.
FileVault 2 encrypts your data.
With FileVault 2, your data is safe and secure — even if your Mac falls into the wrong hands. FileVault 2 encrypts the entire drive on your Mac, protecting your data with XTS-AES 128 encryption. And on Mac systems with an Apple T2 Security Chip, FileVault 2 keys are created and protected by the Secure Enclave for even more security.
Designed to protect your privacy.
The most secure browser for your Mac is the one that comes with your Mac. Built-in privacy features in Safari, like Intelligent Tracking Prevention, help keep your browsing your business. Automatic strong passwords make it easy to create and use unique passwords for all the sites you visit. And iCloud Keychain syncs those passwords securely across all your devices, so you don’t have to remember them. You can also easily find and upgrade any weak passwords you’ve previously used (and reused and reused and reused).
Automatic protections from harmful sites.
Scan Mac For Virus Free

Best Virus Protection For Mac
Safari also helps safeguard you against fraudulent websites and those that harbour malware — before you visit them. If a website seems suspicious, Safari prevents it from loading and notifies you. And when connecting to unencrypted sites, Safari will warn you. So everything you need to browse without worry is right at your fingertips.
Find your missing Mac with Find My.
Best Virus Software For Macbook
The new Find My app combines Find My iPhone and Find My Friends into a single, easy-to-use app on Mac, iPad and iPhone. Find My can help you locate a missing Mac — even if it’s offline or sleeping — by sending out Bluetooth signals that can be detected by nearby Apple devices in use. These devices then relay the detected location of your Mac to iCloud so you can locate it in the Find My app. It’s all anonymous and encrypted end-to-end so no one — including Apple — knows the identity of any reporting device or the location of your Mac. And it all happens silently using tiny bits of data that piggyback on existing network traffic. So there’s no need to worry about your battery life, your data usage or your privacy being compromised.
Recommended Virus Software For Mac Windows 10
Keep your Mac safe.
Even if it’s in the wrong hands.
All Mac models with the Apple T2 Security Chip now support Activation Lock — just like your iPhone or iPad. So if your Mac is ever misplaced or lost, the only person who can erase and reactivate it is you.